How is Automotive Cybersecurity Controlled?
How is Automotive Cybersecurity Controlled?
Unlock Engineering Insights: Explore Our Technical Articles Now!
Discover a Wealth of Knowledge – Browse Our eBooks, Whitepapers, and More!
Stay Informed and Inspired – View Our Webinars and Videos Today!
A 10-question assessment scores your organization across two critical dimensions
6 min read
![]() Kelly Stephenson
:
Jul 27, 2022 3:37:58 PM
Kelly Stephenson
:
Jul 27, 2022 3:37:58 PM
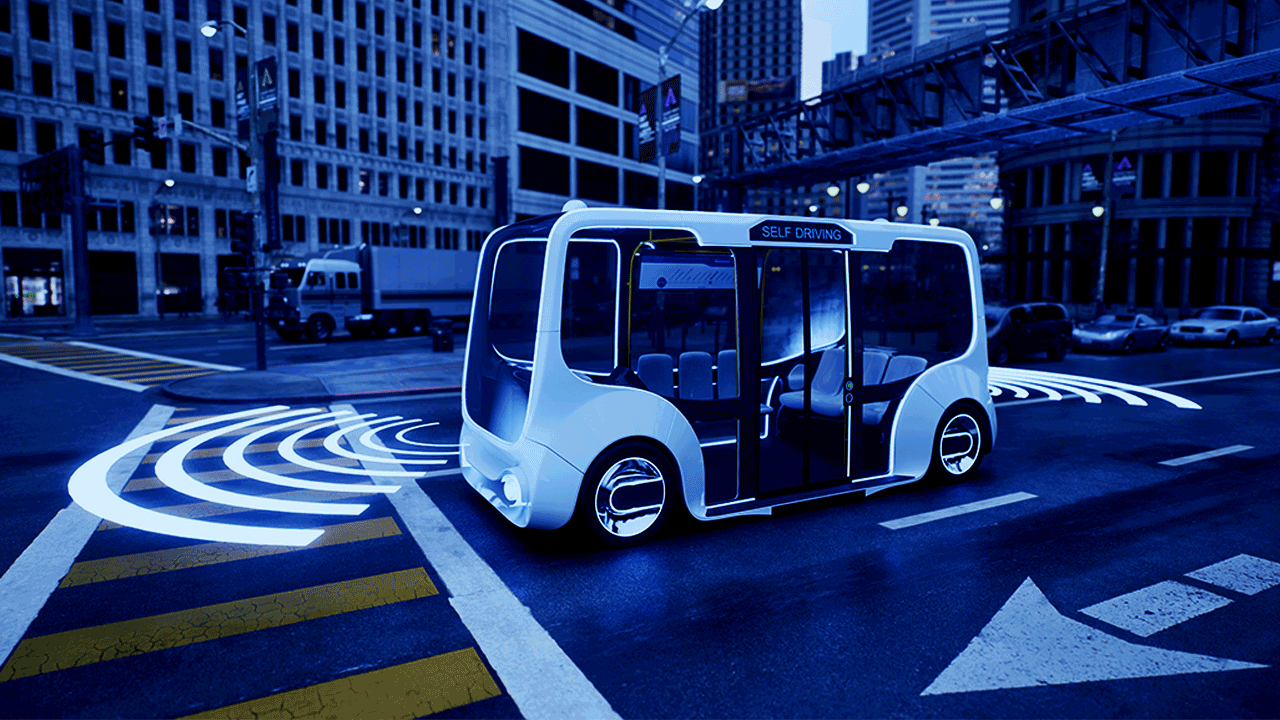
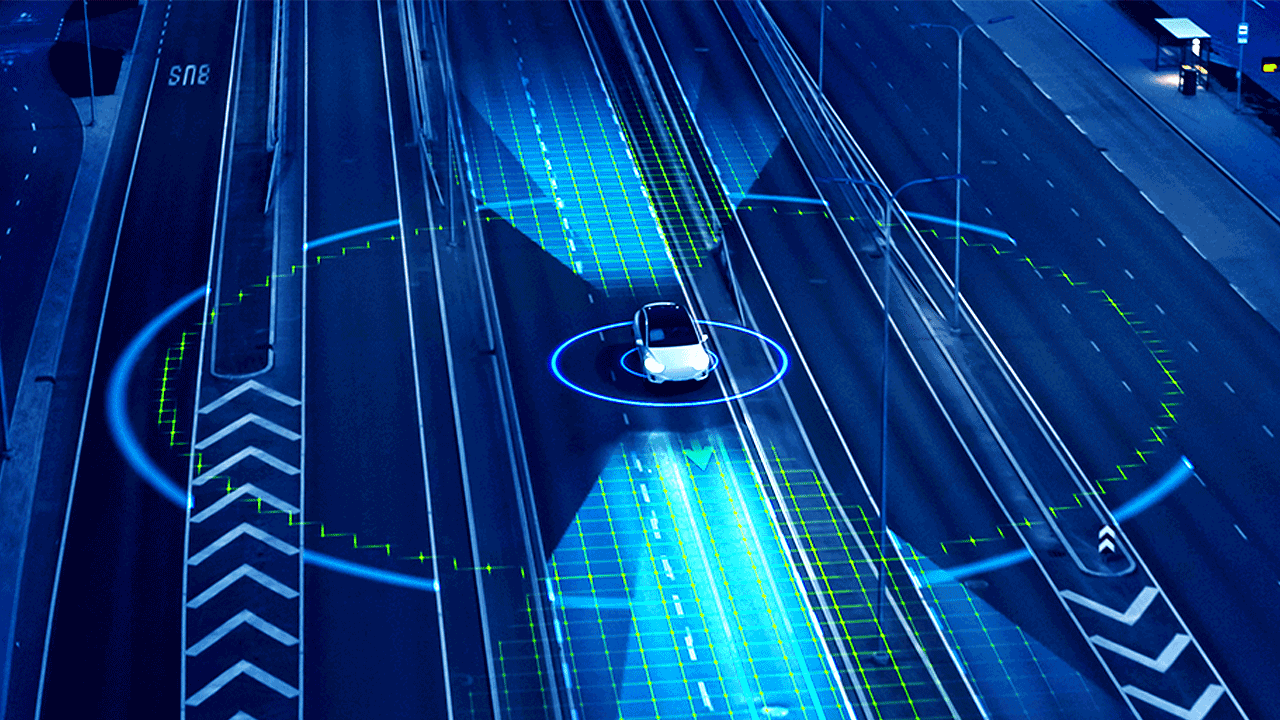
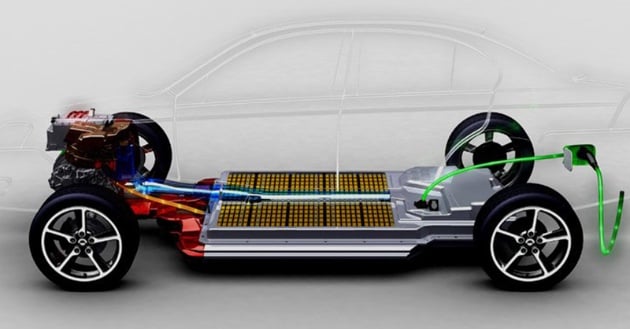
Modern electric vehicles (EVs) are mechatronic machines that combine electric propulsion, electronic control, mechanical actuators, and extensive sensor packages, to create a vehicle that is more intelligent, more efficient, and safer than traditional fossil fuel vehicles. And as they evolve, they are laying the foundations for true autonomous operation. The lifeblood of these systems is the trustworthy communication of data between the driver and the vehicle, the vehicle and its environment, and the transfer of data among the different systems of the vehicle itself. Keeping these communications protected and secure is the role of cybersecurity, which is the practice of protecting sensitive information and critical systems from digital attacks. The cybersecurity of autonomous vehicles is one of the fastest-growing and most important topics in the automotive realm today and is worthy of detailed examination.
Autonomous electric vehicle ecosystems function much like an organism, with different systems working together under rules and conditions that have evolved and been refined over time. It is an efficient system that is built upon the trustworthiness of the data flowing within it. But just like a natural organism, these systems are vulnerable to weakness and exploitation. These risks can take many forms, some random and accidental, and others quite targeted and deliberate.
To keep the vehicle ecosystems healthy and viable, they must be protected. To protect them, the risks must first be identified. Like a natural organism that develops antibodies and grows stronger after an illness, the mechatronic systems of an autonomous EV must be attacked to learn the weaknesses and develop effective corrections and countermeasures. Ideally, these attacks are planned and executed by ethical hackers who work on isolated virtual duplicates of the system where they can experiment and try to break the system without negatively impacting anything in the real world, and then share what they have learned so the issues can be corrected. But too often, the systems are broken by bad actors who simply don’t care about the damage they cause when they break things, or they are trying to do deliberate harm. And occasionally, systems are vulnerable to unintentional risks such as natural disasters, power outages, and service interruptions. Regardless of the cause, all of these are risks that cybersecurity is intended to mitigate.
An autonomous vehicle can be much safer than a traditional car when the system operates as intended. But because so much of the driving burden is shifted from humans to the vehicle, there is a great risk of harm if the system is compromised. One weakness exposed through natural disaster or deliberately exploited, can give a bad actor the power to turn otherwise safe autonomous cars into weaponized machines of terror, or simply render them inoperable, causing great financial harm. This cannot be allowed to happen. Autonomous vehicles must be functionally safe to prevent them from becoming harmful either accidentally or deliberately. Achieving this will not be easy, but it can be done. Robust and consistent cybersecurity practices applied correctly with diligence, provide the step-by-step framework for identifying and managing risk. Minimize the risks, and achieving functional safety becomes possible.
Autonomous and connected vehicles are the product of a complex ecosystem with many elements. Examined in detail, the elements are almost too numerous to count. Each of these is a potential point of weakness and attack, and each one brings with it unique challenges and requirements.
Some aspects of the cybersecurity realm have seen recent breakthroughs, innovations, and other victories. We are certainly seeing more emphasis on cybersecurity in general. And we are seeing cybersecurity mature into a formal initiative within organizations that are now being driven from the top down, pushing the cybersecurity culture harder. Ten years ago, even the better developers didn't care about cybersecurity. Now, we all care about it because we are seeing the results of not caring about it.
In addition, organizations now have standards to rely on that have achieved a higher level of maturity and broad acceptance. These standards are global in scope and come from multiple vetted sources, including the International Organization for Standardization, and the UNECE World Forum for Harmonization of Vehicle Regulations (WP.29):
Beyond the automotive realm, IoT products and gadgets have grown into a huge market. Many have earned a bad reputation because they haven't prioritized cybersecurity until recently, and their products have been exposed as being vulnerable at even the most rudimentary levels. But now, IoT manufacturers are taking cybersecurity more seriously, and these manufacturers are starting to allocate more time and money to the issue and trying to find the right people to help them. A lot of these organizations don't have people on the payroll with the up-to-date cybersecurity knowledge they need. So, they are reaching out to companies like LHP, and then asking, "Hey, I've got this embedded gadget. What does cybersecurity mean to me?" We are seeing many more of those conversations. And we're starting to see manufacturers allocate the right amount of time and resources to make their products more secure and for their company to remain competitive.
Cybersecurity considerations must be woven into the product development process from the start. If it isn’t, it can cause real problems. For example, if a company approaches LHP with questions about cybersecurity and we determine that there are several security requirements that they must start implementing into their firmware, and they have already set their firmware development schedule before they talked to us, that’s a problem. We know that dates are going to have to be pushed out, to circle back and do the proper cybersecurity work that should have been done from the start.
To rectify this, we are now starting to see those conversations much earlier in the development cycle instead of at the end. Big OEMs now are building up their cybersecurity capability. They are hiring cyber folks like crazy trying to build their teams up and build those procedures up into a mature process. Much like the realm of functional safety had to evolve and mature, so we are starting to see an understanding that cybersecurity is part of any business that manufactures or services connected products.
The evolution of cybersecurity toward maturity is a big deal. We are moving from a world where, during the development of a product the cybersecurity people must prove to the product designers that cybersecurity is needed, to flipping the tables and making the product designers prove to the cybersecurity people that it is not needed. As this knowledge and understanding are cascaded throughout the automotive realm, project managers are much better informed and not as likely to automatically reject a security requirement.
This is a significant change for the better. Only a few years ago, if a project manager didn’t care about security, they would just reject all the security requirements. The project manager would tell the cybersecurity people that they must prove, through a large volume of additional work, that the company must perform all this cybersecurity work. Because most project managers didn’t know how developers did this work, and because they didn’t plan for it, they didn't schedule for it.
Today, we are seeing more acceptance of the importance of cybersecurity. It is being integrated into the whole development process. That is an exciting change for the industry, as in the past that level of understanding hasn't been there. This shift is recent. In the last 5-10 years or so, we've seen more interfacing with security folks, more learning, more understanding, and therefore more cooperation and support.
Although there has been much progress, there are still some project managers out there that like to argue with you. But that is acceptable. We, as security engineers, should provide the evidence to show that cybersecurity is needed. We don't want to prescribe piles of security requirements that don't provide value to the company or the assets that you are trying to protect. When a security engineer tells somebody that a requirement is needed, we must provide evidence to the business to show that it is needed.
The conversations are getting better. Now, it is not just the security folks trying to push security in the organization, but individual developers. When we inform them of a security requirement that is absolutely needed, quite often they now agree and admit that they have had similar conversations in their own circles. They know the organization must figure out how to make it work, but they couldn't get a resolution. So, they're thinking about it, but they're not pushing it.
At this point, it is our job to come in and say, “This must be done.” And we were finally able to get them to resolve it. It was just a matter of getting all the right people together and having a conversation to make sure that we could get that requirement resolved.
Cybersecurity is too important to be allowed to languish. The movement must always be forward. And productive cooperation makes progress possible. It makes sense for the business, and it's all we're asking.
How is Automotive Cybersecurity Controlled?
What are the cybersecurity challenges for Connected and Autonomous Vehicles?
As vehicle technology advances to include more autonomy and higher degrees of connectivity, the number of electronic control units (ECUs) and overall...

Will Autonomous and Electric Vehicles Kill the Fuel Industry? Did you know the first electric vehicle was introduced more than 100 years ago? Today,...
What is Automotive Cybersecurity? Defining cybersecurity To best understand automotive cybersecurity, it is helpful to review the unique...
When Toyota launched the first Prius in 1997, many consumers probably didn’t imagine that just 20 short years later the electric- and hybrid-vehicle...