How is Automotive Cybersecurity Controlled?
How is Automotive Cybersecurity Controlled?
Unlock Engineering Insights: Explore Our Technical Articles Now!
Discover a Wealth of Knowledge – Browse Our eBooks, Whitepapers, and More!
Stay Informed and Inspired – View Our Webinars and Videos Today!
A 10-question assessment scores your organization across two critical dimensions
5 min read
![]() Kelly Stephenson
:
Aug 9, 2022 3:13:40 PM
Kelly Stephenson
:
Aug 9, 2022 3:13:40 PM
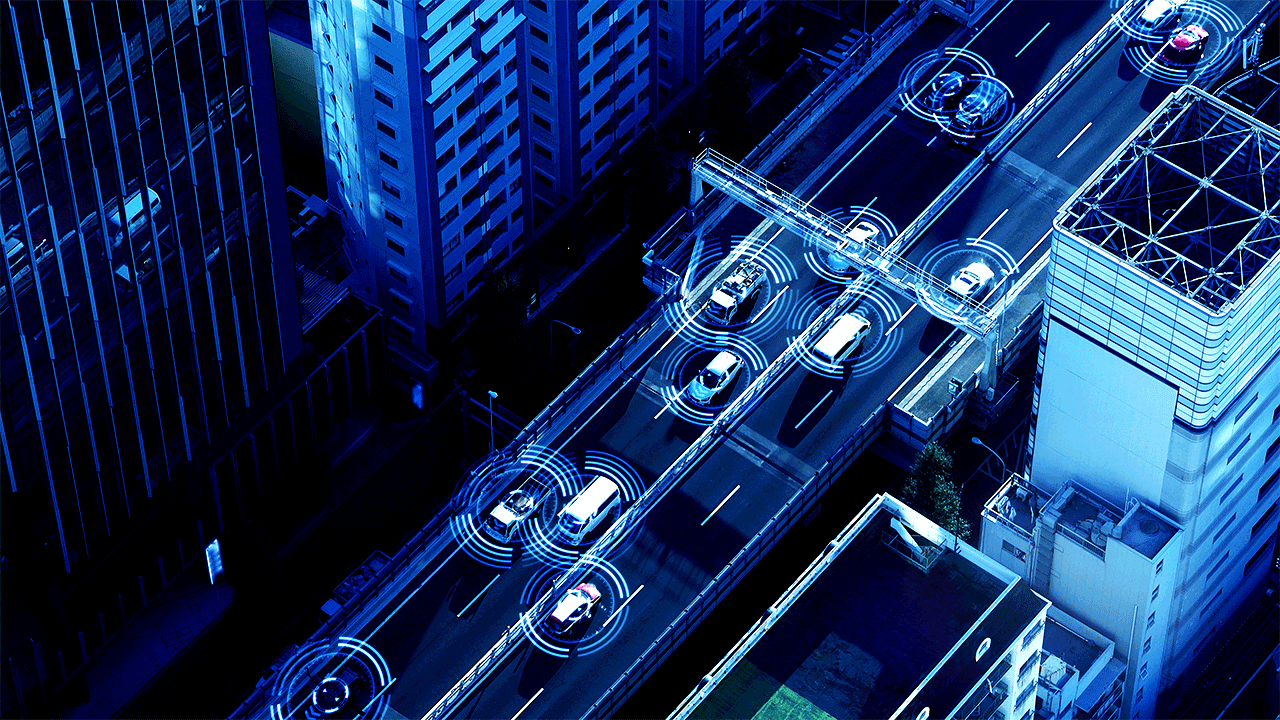
The cybersecurity challenges presented by autonomous and connected vehicles offer a wide array of learning opportunities. Skills from a variety of disciplines can be applied to solving these problems. While this knowledge plays a critical role, perseverance and an insatiable desire to take things apart and find out how they tick can be the most powerful cybersecurity tools of them all.
The automotive realm is certainly no stranger to people testing the limits of their vehicles, trying to break things, getting to know their cars from the inside out, and then modifying them. That's the very definition of an automobile mechanic from the first days of vehicles. These days, there are a lot of parallels between hardware folks and software folks who are all trying to take the cars apart and figure out how they tick. The two play nicely together because it's the same kind of mindset.
If you understand the vehicle communication lines and buses and the way data is transferred back and forth, those transfer technologies are not very specific to the automotive industry. For example, the Controller Area Network (CAN bus) protocol is a robust vehicle bus standard that allows microcontrollers and other devices to communicate with each other's applications without a host computer. Though the CAN Bus originated in the automotive industry, it is now utilized in many other products. CAN Busses are now common in both industrial and automotive applications and can even be found in 3D printers.
In contrast, other protocols utilized in vehicles, such as the Media Object Server Transport (MOST) protocol, can be very specific to the automotive industry. The ECUs in modern vehicles control nearly all functions, including engine control, electronic fuel injection (EFI), anti-lock braking system, transmission, door locks, window operation, and more. Systems such as the Local Interconnect Network (LIN Bus) protocol, and the MOST protocol, are specific to the automotive industry. A person new to this realm would have to dive in and learn these protocols.
An especially important protocol to learn is the Unified Diagnostic Services (UDS) protocol, which is used in ECUs within automotive electronics and is specified in ISO 14229. It is an international standard protocol, not company-specific. It is used in all new ECUs made by Tier 1 OEMs and is incorporated into other standards, such as AUTOSAR.
You must really dive into the fine details and understand these protocols from the bottom up to learn how to break them. For example, a lot of people have broken the UDS Security Access Service Identifier (0x27) because it's not as secure as the Service Identifier (0x29), which updated the standard in 2020 and enabled more modern methods of authentication, including bidirectional authentication with PKI-based Certificate Exchange. That's an example of the level of detail and the kind of things that you need to understand.
The electronics in a car can be categorized as either electrical, mechanical, or computer controls. They interact with each other, but typically they each have independent computer systems. As vehicle systems become more connected, they become more complex.
As the automotive industry moves toward implementing an automotive ethernet, the lines between automotive-specific systems and computer network systems are going to get blurred a little bit. People already understand the kind of ethernet used in a home or office. But in a car, it is a priority for systems to be optimized to save weight and to be deterministic by utilizing Time Sensitive Networking (TSN) to achieve the time-sensitive transmission of data over deterministic Ethernet networks.
Automotive ethernet cable is physically different. It is a single unshielded copper twisted pair, making it low in weight and cost less to manufacture than traditional ethernet cable. Unlike standard ethernet, which contains two twisted pairs of dedicated wires, one for transmission and the other for the reception, automotive ethernet has a single twisted pair that is used for both transmit and receive operations at the same time. In automotive ethernet, both ends of the connection must employ a hybrid transceiver that is capable of distinguishing between what it is being sent versus what it is receiving. But the automotive ethernet system is still sending packets across, using the same protocols. Given the increasing bandwidth needs of today’s connected systems and the fact that modern complex wiring harnesses can account for up to 1/3 of the price of a new car and over 130 pounds of its weight. Thus, being able to reduce the number of wires in a vehicle is an improvement that is well worth pursuing.
This demonstrates how the lines are blurring, where some skills will play a role in both the traditional networking realm and in the automotive networking space. There are already people who understand networking, from their experience connecting to servers and hacking and breaking those systems. They are going to find that their skills are becoming more useful in the automotive space.
Several Infotainment systems in vehicles run Linux operating systems. These are operating systems that folks have been hacking and breaking for many years, with a lot of the servers running Linux. These are skill sets that people can use to start cracking and hacking automotive spaces.
Automotive systems are becoming less unique. Bluetooth, USB, WiFi... these are all standard protocols that a lot of people have used for different applications. For a vehicle, you might say that we're blurring a fine line between automotive systems and standard computer systems.
If a bad guy wanted to break into ECUs or IoT devices, they would need to understand the system and possess the skills for studying hardware, as they function like an analyzer to capture that data to see if they can break it. That is a hardware level of understanding that a lot of people just don't have. They can be familiar with the protocols, hacking the protocols to try to break into the system, but unless they have a hardware engineer’s level of knowledge, somebody that really understands electrical engineering, they really don't understand how the hardware works.
At LHP, we are focusing on the embedded-side devices, hardware security, and understanding how to make sure that if somebody does break into these devices, they're not pulling secrets out. These specialized ECU or ECM domain controllers are protected. And some of those security protections may not exist in the IT world. So, we place limitations at the hardware level, and we try to make sure that these security mechanisms get turned on properly, and that they're running and put in place.
If you think about a server, it could consist of a big computer running several processors, and it may have a Hardware Security Module (HSM). But, HSMs are now starting to show up in some vehicle ECUs and domain controllers as well. There can be a lot of HSMs, or sometimes there aren’t any. How can this device be secured if it doesn't have a good, secure enclave for storage? You have to understand how to implement that, too.
Vulnerabilities are now coming left and right, making cybersecurity considerations something that can no longer be ignored. We are seeing a greatly increased interest in automotive cybersecurity, and likewise an increased effort around breaking everything in it. Twenty years ago, only a few people tried to hack anything. Today, hacking is a widely popular activity, and the people doing it are motivated, enthusiastic, smart, and skilled. Hackers want to test and break everything. They want to break it all. This is the reality that we now live in.
Defense in depth is a frequent topic of cybersecurity conversations. Simply put, defense in depth is where we try to aggravate the attacker with multiple levels of defense, to get him to the point where he just finally gives up in frustration. We know that no matter what we do, a determined person can hack into these systems and crack them open if they devote enough time and resources to the task. We want to make it so painful and unprofitable both financially and motivationally, that they just finally decide that they are not going to put any more time or effort into it. We want them to give up and go investigate something else that is much easier and more rewarding to get to. That is a legitimate security strategy because no product can be guaranteed secure 100%.
Why is Cybersecurity Important for Autonomous Vehicles?
What Can Be Done to Secure Autonomous Vehicles from Cyber Attacks?
How is Automotive Cybersecurity Controlled?
Why is Cybersecurity Important for Autonomous Vehicles? Introduction Modern electric vehicles (EVs) are mechatronic machines that combine electric...

LHP will be at the 2018 IoT Solutions World Congress Showcasing Embedded Cybersecurity On a Vehicle Platform

Framework for automotive cybersecurity This is Part 3 of a three-part blog series on automotive cybersecurity. If you have not yet read Part 1:...

Cybersecurity and the automotive supply chain
As vehicle technology advances to include more autonomy and higher degrees of connectivity, the number of electronic control units (ECUs) and overall...